More than 90% of organizations use open source in their applications, and with good reason. But along with a multitude of benefits, open source does carry license compliance and security risks.
Traditionally, open source vulnerability management tools (like software composition analysis) have largely focused on identifying and mitigating CVEs (Common Vulnerabilities and Exposures). But it is becoming increasingly clear that focusing on CVEs — without accounting for other security risks impacting open source — can leave organizations vulnerable. As recent supply chain attacks have proven, the surface area of attacks has expanded, with bad actors finding novel attack vectors to infiltrate and inject malware into applications. These include:
Stale Packages: This refers to the scenario where an organization uses a package that is a number of versions behind the current version. This can leave it susceptible to vulnerabilities.
Abandonware: A package is considered abandoned when it hasn’t been updated for an extended period of time or the maintainer(s) are no longer responsive. This signals that maintainers are likely not going to patch bugs or introduce new features. If there is a vulnerability in this package, it is unlikely to be patched.
Native Binary Code: These binaries can be used as a vector to cause potentially malicious behavior.
Empty Packages: Dependencies that do not contain any code, which may be indicative of:
- A package that has been removed from a registry
- A package that's been misconfigured or erroneously published
- Name squatting
While these are not immediately concerning, it is possible that an author can use these to publish a version with malicious code at a later date.
The CVE mechanism isn’t set up to handle these novel types of security gaps that can cause various security risks. Teams need a more proactive approach to identify and mitigate these risks and strengthen software supply chain security.
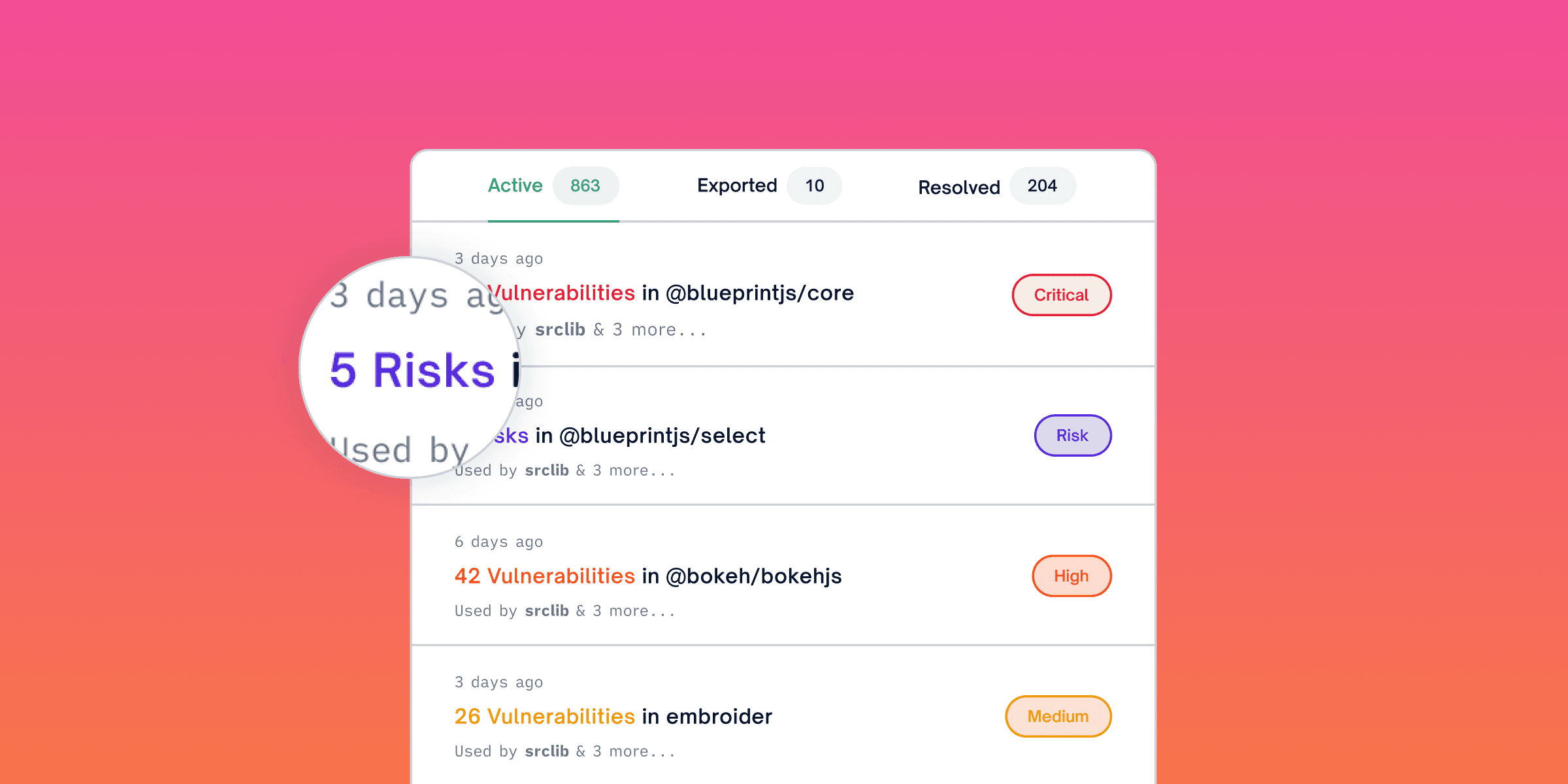
Introducing FOSSA Risk Intelligence
We are excited to announce the private beta of our Risk Intelligence add-on to harden your software supply chain. This add-on provides proactive and comprehensive defense to your applications against sophisticated attack vectors that cannot be addressed via CVEs. Teams are able to identify and address operational risks in their software supply chain like:
- Stale Packages
- Abandonware
- Empty Package
- Native Code
Stale Packages: Users can configure how many major and minor versions behind the latest version of the package is acceptable to your organization. This will ensure that there are no stale or outdated packages for any of your dependencies. You can also use this to ensure that your applications are using the latest/safest version of any library.
Empty Packages: Enabling this signal within the security policies ensures that packages with no code will be marked as risky, so you can keep them out of software.
Abandonware: Users are notified if their projects have abandoned packages (defined as not being updated in two-plus years).
Native Code: Customers are alerted about any unexpected executables within their packages.
Bring Risk Intelligence to Your Organization
FOSSA Risk Intelligence is currently in private beta, and we encourage Vulnerability Management users on business and enterprise plans to consider joining.
Please sign up to be a part of the beta here, and contact us with any questions or feedback at support@fossa.com. We look forward to working with beta members to ensure we continue to build functionality that meets their needs and provides significant value.